| iOS App Attest | Android Play Integrity |
|---|---|
| Apple-signed device key bound to your app | Google-signed integrity verdict for your app |
Use cases
Attestation is opt-in and a general recommendation for production apps.Production mobile apps
For any live app handling real user wallets or assets.
High-security environments
Block spoofed or tampered clients from authenticating.
Multi-platform apps
Apply attestation to mobile while securing web separately with domain configuration.
Attestation has no effect on web apps. To secure your web surface, configure your allowed domains in Domain Allowlisting.
What is protected
Attestation is enforced at authentication. Since all wallet operations require an authenticated session, attestation effectively protects every action in your app. When attestation is configured in the CDP Portal for your app, the CDP backend requires valid proof at login and rejects any request that cannot provide it. The protection is entirely server-side and transparent to your users.Getting started
iOS App Attest
Set up Apple App Attest for iOS apps
Android Play Integrity
Set up Google Play Integrity for Android apps
Portal configuration
Before enabling attestation, configure your app’s identity in the CDP Portal. Navigate to your project, open the Security tab, and add your mobile app in the Client configuration section.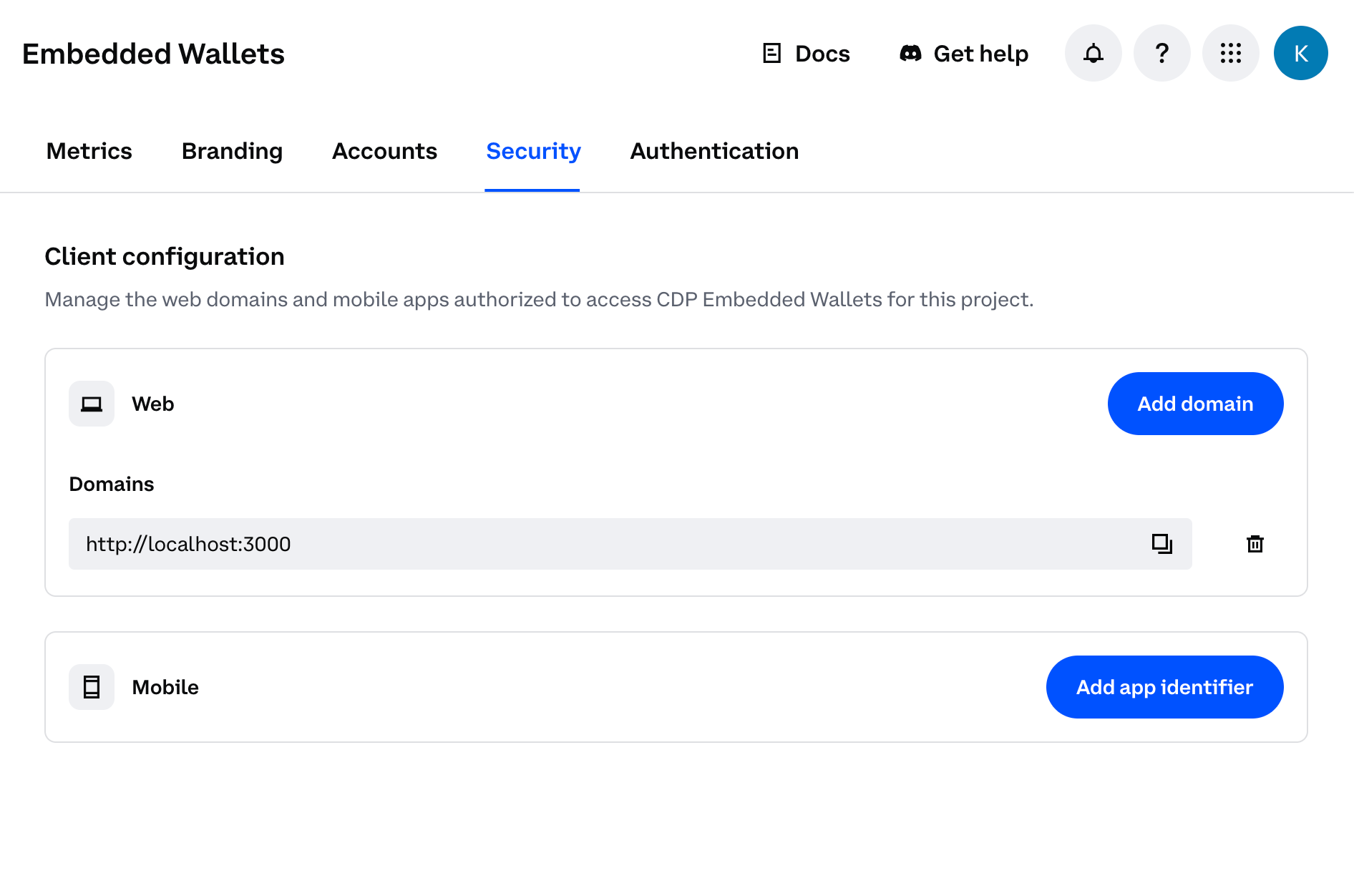
Add iOS entry
Click Add app identifier and follow the steps to configure your iOS application.
You will need:
- Apple Team ID - found in Xcode under Signing & Capabilities (e.g.
ABC123DEF4) - Bundle ID - the bundle identifier of your app (e.g.
com.example.myapp)
teamID.bundleID format (e.g. ABC123DEF4.com.example.myapp). The Team ID must be exactly 10 alphanumeric characters and the bundle ID must be dot-separated alphanumeric segments. The portal will reject invalid formats.See the iOS setup guide for details.Add Android entry
Click Add app identifier and follow the steps to configure your Android application.
You will need:
- Package name - the application ID of your app (e.g.
com.example.myapp) - Google Cloud project number - found in Google Cloud Console → Project Settings
- Service account JSON - credentials for a service account that has the Play Integrity API permission
Each platform supports a maximum of 10 entries. Duplicate identifiers are not allowed.
Authentication errors
If attestation fails (for example, due to a misconfigured bundle ID in the portal, a missing import in your client code, or a device that cannot produce a valid token), users will see a generic authentication error. If your users encounter unexpected authentication errors after enabling attestation, check:- The bundle ID (iOS) or package name (Android) in your CDP Portal project settings matches what is compiled into your app.
- The
@coinbase/cdp-app-attestimport is present in your app entry point. - On Android, the app was installed via the Play Store.
Enabling attestation in the portal takes effect immediately. Ensure the updated app version with
@coinbase/cdp-app-attest installed and imported is fully rolled out to all your users before enabling attestation in the portal. If attestation is enabled while users are still on an older version without the package, they will experience authentication errors.What to read next
- iOS App Attest — set up attestation for iOS
- Android Play Integrity — set up attestation for Android
- React Native Quickstart — get started with user wallets in React Native