Overview
Auth method linking enables users to associate multiple authentication methods with a single user wallet account. This allows users to sign in using different methods (email, SMS, OAuth) while maintaining access to the same wallet and user identity.Why link authentication methods?
By default, each authentication method creates a separate user identity. For example, if a user signs in with their email and later signs in with their phone number, they would have two different user wallets. Auth method linking solves this problem by allowing users to:- Access their wallet using multiple methods: Sign in with email, phone, or social providers interchangeably.
- Meet 2FA requirements: For applications that require 2FA, CDP wallets provide a smooth integration.
- Improve account security: Add additional authentication factors as users accumulate more funds.
- Enhance account recovery: Multiple methods provide backup options if one method becomes unavailable.
Supported authentication methods
You can link any combination of the following authentication methods to a single user account:- Email OTP
- SMS OTP
- All supported OAuth providers
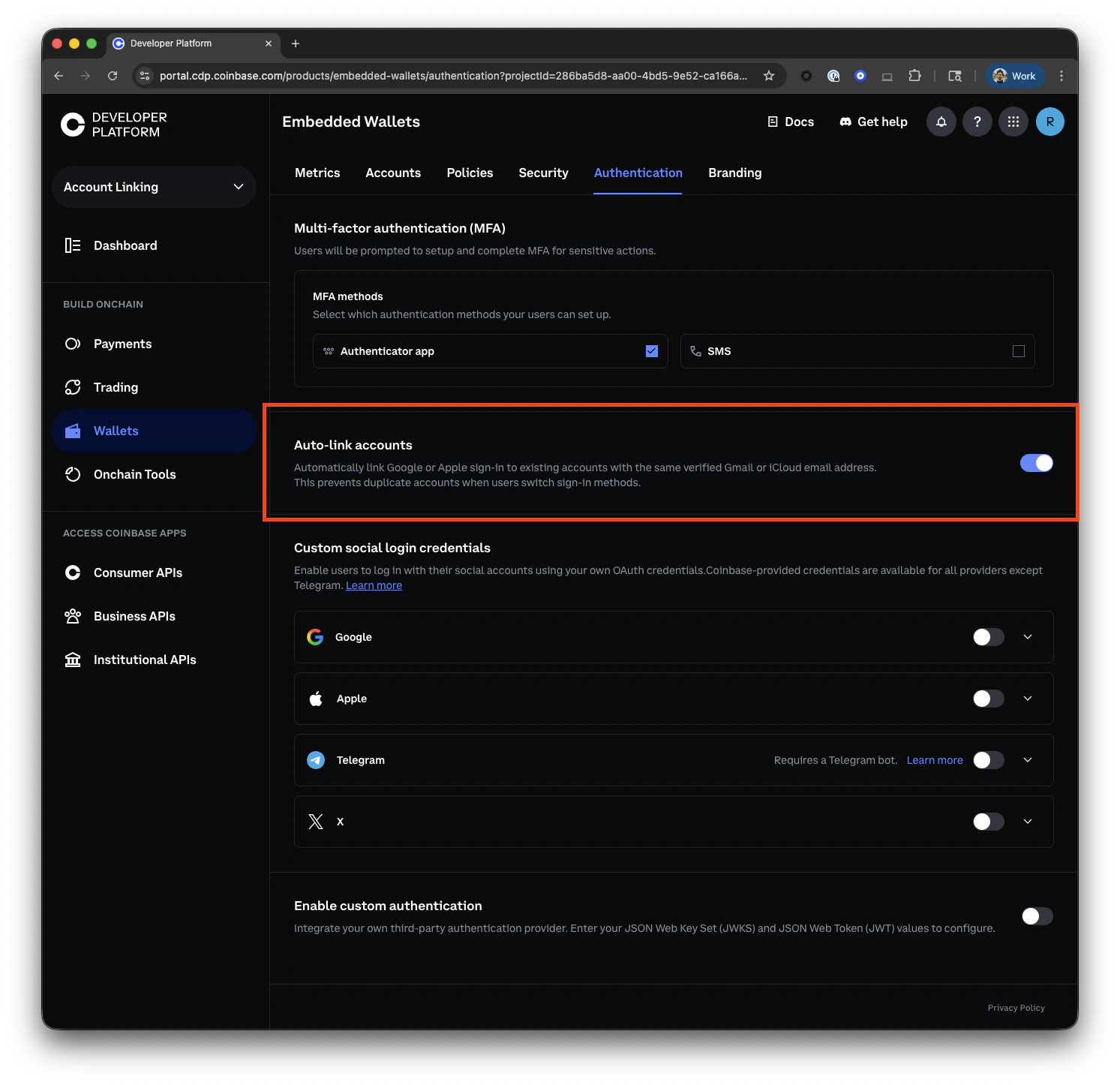
Auto-linking accounts
Auto-linking automatically connects a user’s Google or Apple sign-in to an existing account that shares the same verified email address. This prevents duplicate accounts when users switch between sign-in methods — for example, a user who originally signed up with their Gmail address via email OTP can later sign in with Google OAuth and land in the same wallet, without any manual linking step.How it works
When a user signs in for the first time with Google or Apple OAuth (or with a Gmail/iCloud email address), the system checks whether an account already exists under a linked auth method before creating a new one. Two scenarios are covered:| Sign-in method | Trigger condition | Auto-link target |
|---|---|---|
| Google or Apple OAuth | No existing account found for the OAuth subject | Existing email-OTP account with the same verified @gmail.com / @icloud.com address |
Email OTP (@gmail.com / @icloud.com) | No existing account found for the email address | Existing Google or Apple OAuth account with the same email address |
Auto-linking only applies to Google (
@gmail.com) and Apple (@icloud.com). Other OAuth providers and email domains are not eligible.Requirements
For auto-linking to trigger, all of the following must be true:- Auto-linking is enabled in your project settings (see below).
- The OAuth provider is Google or Apple.
- For OAuth sign-in: the email returned by the provider is verified and uses the provider’s expected domain (
@gmail.comor@icloud.com). - No existing account is already registered under the OAuth subject ID — auto-linking only runs when a new account would otherwise be created.
Enabling auto-linking
Toggle auto-linking on or off from the CDP Portal Authentication settings:- Open the Authentication tab for your project.
- Find the Auto-link accounts section.
- Enable the toggle.
Security features
Auth method linking maintains the same security standards as initial authentication:Verification requirements
Verification requirements
Each additional authentication method must be verified before being linked:
- Email: Requires OTP verification (10-minute expiration).
- SMS: Requires OTP verification (5-minute expiration).
- OAuth providers: Requires successful OAuth flow completion.
Rate limiting
Rate limiting
- Protection against brute force attempts on OTP verification.
- Failed attempts may temporarily lock linking operations.
Device binding
Device binding
- Linked methods maintain the same device binding as the primary authentication.
- Users can access their wallet from up to 5 devices regardless of which linked method they use.
Implementation examples
The examples below show both React component and hook-based approaches from
@coinbase/cdp-react and @coinbase/cdp-hooks. For other implementation approaches, see the Implementation Guide.Using React components
Basic usage
Render aLinkAuth component with an onLinkSuccess handler:
Accessing state
Display a message based on the LinkAuth state:Advanced example: Using SignInModal
Customize LinkAuthItems to show a modal for non-OAuth methods instead of transitioning in place:Using React hooks
Link an email address
Use theuseLinkEmail hook to link an email address to the currently authenticated user. This follows the same two-step flow as email sign-in: initiate the flow and then verify the OTP.
Link a phone number
Use theuseLinkSms hook to link a phone number to the currently authenticated user. Like email linking, this requires OTP verification.
Link a Google account
Use theuseLinkGoogle hook to link a Google account to the currently authenticated user. This initiates the OAuth flow for Google authentication.
Link an Apple account
Use theuseLinkApple hook to link an Apple account to the currently authenticated user. This initiates the OAuth flow for Apple authentication.
Link an X account
Use theuseLinkOAuth hook to link an X account to the currently authenticated user. This initiates the OAuth flow for X authentication.
Link a Telegram account
Use theuseLinkOAuth hook to link a Telegram account to the currently authenticated user. This initiates the OAuth flow for Telegram authentication.
Link any OAuth provider
Use theuseLinkOAuth hook to link any supported OAuth provider to the currently authenticated user. This provides a unified interface for all OAuth providers.
User experience best practices
When implementing auth method linking, consider these UX recommendations:Progressive security
Progressive security
Prompt users to add additional authentication methods as their account value increases. For example:
- Basic users: Single authentication method.
- Users with funds: Prompt to add a second method.
- High-value accounts: Encourage multiple authentication methods.
Clear communication
Clear communication
- Explain the benefits of linking additional methods before prompting.
- Show which methods are already linked in account settings.
- Provide clear success/error messages during the linking process.
Account recovery
Account recovery
- Position linked methods as a recovery option.
- Encourage users to link at least one additional method for account security.
- Provide clear documentation on how to use linked methods for sign-in.
Onramp integration
Onramp integration
For apps integrating with Coinbase Onramp:
- Inform users they need both email and phone verification for onramp.
- Automatically prompt for the missing method when users attempt to use onramp.
- Provide a seamless flow from authentication to onramp.
Error States
Common errors you may encounter when linking authentication methods:| Error | Description |
|---|---|
METHOD_ALREADY_LINKED | The authentication method is already linked to this or another account. |
ACCOUNT_EXISTS | The intended account to link already belongs to another user. |
What to read next
- Authentication Methods: Learn about available authentication methods
- React Hooks: Comprehensive guide to CDP React hooks
- Onramp Integration: Integrate Coinbase Onramp with linked authentication
- Session Management: Understand how sessions work with linked methods
- Best Practices: Security recommendations for production applications